Мы не храним никаких логов, которые позволили бы нам или третьим лицам связать IP-адрес в конкретном промежутке времени с пользователем нашего сервиса. Единственные данные, которые мы храним — это e-mail и имя пользователя, но невозможно связать деятельность пользователя в интернете с конкретным юзером нашего сервиса.
Мы не находимся ни под чьей юрисдикцией. Нет таких обстоятельств, которые заставили бы нас предоставить информацию о наших юзерах. Если закон заставит нас сделать это, мы переместим свой бизнес в такую страну, где это не будет действовать, а если и это не сработает, мы просто закроемся до того, как предоставим какую-либо информацию.
Мы не можем соответствовать DMCA, поскольку у нас просто нет возможности сделать что-то с нашими юзерами. Поскольку у нас нет логов, мы не можем связать их с пользователями для ответных действий.
Сейчас мы принимаем платежи через Bitcoin, Perfect Money, Webmoney, EgoPay и ИнтерКасса. Мы создаем уникальный ключ для транзакции, чтобы убедиться, что платеж за аккаунт прошел. После этого мы удаляем ключ, так что платеж никак нельзя связать с конкретным IP. Кроме того, мы хотели бы склонить наших юзеров к использованию анонимных e-mail и оплате через Bitcoin, чтобы обеспечить ещё более высокий уровень анонимности. Мы сохраняем минимальную информацию о пользователе, которая необходима для платежа.
Нет, в случае одновременного подключения. При одновременном подключении сервер автоматически отключит одно из подключений. Но если у вас компьютерная сеть, то вы можете организовать подключение к VPN-серверу с одного компьютера-сервера, а остальные компьютеры могут просто выходить в Интернет через компьютер-сервер. Либо настроить подключение к VPN серверу через ваш роутер (если он подерживает VPN сессии).
Категорически запрещено использование наших серверов в незаконных целях, т.к. это способствует поступлениям жалоб на наши сервера, в следствии чего, они будут отключены. Это затруднит предоставление качественных услуг нашим клиентам. Советуем внимательно прочитать п.2.2.7 “Пользовательского соглашения”, при не соблюдении данных правил, сервис в праве отказать в обслуживании без возврата средств и дальнейшего предоставления доступа.
Вам предоставляется право выбирать любой сервер и IP адрес в рамках вашего тарифа, вы можете менять сервера и IP адреса сколько угодно, это всегда будет бесплатно.
OpenVPN - свободная реализация технологии VPN с открытым исходным кодом для создания зашифрованных каналов типа точка-точка или сервер-клиенты между компьютерами. Она позволяет устанавливать соединения между компьютерами, находящимися за NAT-firewall, без необходимости изменения их настроек. OpenVPN была создана Джеймсом Йонаном (James Yonan) и распространяется под лицензией GNU GPL. PPTP (Point-to-Point Tunneling Protocol) - туннельный протокол типа точка-точка, позволяющий компьютеру устанавливать защищённое соединение с сервером за счёт создания специального туннеля в стандартной, незащищённой сети. PPTP помещает (инкапсулирует) кадры PPP в IP-пакеты для передачи по глобальной IP-сети, например Интернет. PPTP может также использоваться для организации туннеля между двумя локальными сетями. РРТР использует дополнительное TCP-соединение для обслуживания туннеля. L2TP/IPsec - L2TP поверх IPsec является более защищенным расширением протокола PPTP. Встроен во все современные операционные системы и VPN-совместимые устройства, и так же легко может быть настроен как и PPTP (обычно используется тот же клиент). Может быть немного медленнее, чем PPTP. За NAT может работать некорректно. Подключения к Интернет, которые имеют "белый", реальный IP-адрес (смотря как выдает провайдер), проблем с L2TP не знают.
TCP — «гарантированный» транспортный механизм с предварительным установлением соединения, предоставляющий приложению надёжный поток данных, дающий уверенность в безошибочности получаемых данных, перезапрашивающий данные в случае потери и устраняющий дублирование данных. TCP позволяет регулировать нагрузку на сеть, а также уменьшать время ожидания данных при передаче на большие расстояния. Более того, TCP гарантирует, что полученные данные были отправлены точно в такой же последовательности. В этом его главное отличие от UDP. UDP — протокол передачи датаграмм без установления соединения. Также его называют протоколом «ненадёжной» передачи, в смысле невозможности удостовериться в доставке сообщения адресату, а также возможного перемешивания пакетов. В приложениях, требующих гарантированной передачи данных, используется протокол TCP. UDP обычно используется в таких приложениях, как потоковое видео и компьютерные игры, где допускается потеря пакетов, а повторный запрос затруднён или не оправдан, либо в приложениях вида запрос-ответ (например, запросы к DNS), где создание соединения занимает больше ресурсов, чем повторная отправка.
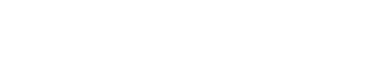
RSA - TLSv1, cipher TLSv1/SSLv3 DHE-RSA-AES256-SHA, 4096 bit
ECC - TLSv1.2, cipher TLSv1/SSLv3 ECDHE-ECDSA-AES256-GCM, 384 bit
ECC (Elliptic Curve Cryptography) - один из самых мощных алгоритмов шифрования, который является намного более криптостойким чем RSA, а так же менее требователен к железу. Мы используем самую надёжную формулу кривой secp256k1, а так же, вместо обычного DHE, мы стали использовать ECDHE (Elliptic Curve Diffie-Hellman with Forward Secrecy).
Wikipedia:
ECC (Elliptic Curve Cryptography) Асимметричная криптография основана на сложности решения некоторых математических задач. Ранние криптосистемы с открытым ключом, такие как алгоритм RSA, криптостойки благодаря тому, что сложно разложить составное число на простые множители. При использовании алгоритмов на эллиптических кривых полагается, что не существует субэкспоненциальных алгоритмов для решения задачи дискретного логарифмирования в группах их точек. При этом порядок группы точек эллиптической кривой определяет сложность задачи. Считается, что для достижения такого же уровня криптостойкости как и в RSA, требуются группы меньших порядков, что уменьшает затраты на хранение и передачу информации. Например, на конференции RSA 2005 Агентство национальной безопасности объявила о создании “Suite B”, в котором используются исключительно алгоритмы эллиптической криптографии, причём для защиты информации классифицируемой до “Top Secret” используются всего лишь 384-битные ключи.

 Tor v3
Tor v3 @FVPNS
@FVPNS

 82822222
82822222 EN
EN RU
RU